COBIT 5 Framework explained

COBIT 5 Framework: this article provides a practical explanation of the COBIT 5 Framework. Next to what it is, this article also highlights Governance of Enterprise IT (GEIT), COBIT 5 Framework Principles, the Seven enablers, the Advantages of this framework and a short summary. After reading, you’ll have a basic understanding of this management process. Enjoy reading!
What is the COBIT 5 Framework?
COBIT 5 is a framework for managers for managing information technology. COBIT stands for Control Objectives for Information and Related Technology. It has been designed as a tool to bridge the gap between technical issues, risks, and control objectives.
COBIT 5 is a recognised guideline and can be applied to pretty much any organisation in any industry. COBIT 5 guarantees the quality, control, and reliability of the information systems within organisations. The goal of COBIT is to optimise the Governance of Enterprise IT (GEIT)
COBIT is used all over the world by different organisations because it offers a manual to create added value and manage risks. Properly functioning and efficient information technology solutions are very important for organisations. It helps ensure that the right information reaches the right places at the right time, supporting internal decision making.
It also helps towards achieving strategic planning goals. In turn, organisations have to keep the risks at acceptable levels and optimise IT processes. Moreover, they need to comply with laws and regulations.
COBIT was introduced by the ISACA in 1996. It was originally intended to be able to manoeuvre better in the world of IT and only consisted of a few control objectives. Today it goes beyond that, and has been implemented in the majority of businesses.
COBIT 5 was released in 2012 and is based on five principles. It has been designed to work with other IT solutions and methods such as COSO and BiSL.
Governance of Enterprise IT (GEIT)
Governance of Enterprise IT (GEIT) is a corporate governance discipline. The discipline is aimed at information and technology within the organisation, particularly performance and risk management.
The increasing interest for IT governance is the result of the increased use of IT solutions and the need of organisations to create value across the entire value chain. Governance for information technology arose from the principles of Total Quality Management (TQM).
Governance for information technology applies to everyone in the organisation: personnel, customers, investors, governance, management, and other stakeholders. It’s used to identify the IT mechanisms and to link these to oversight, in order to manage the risks that result from the use of information technology.
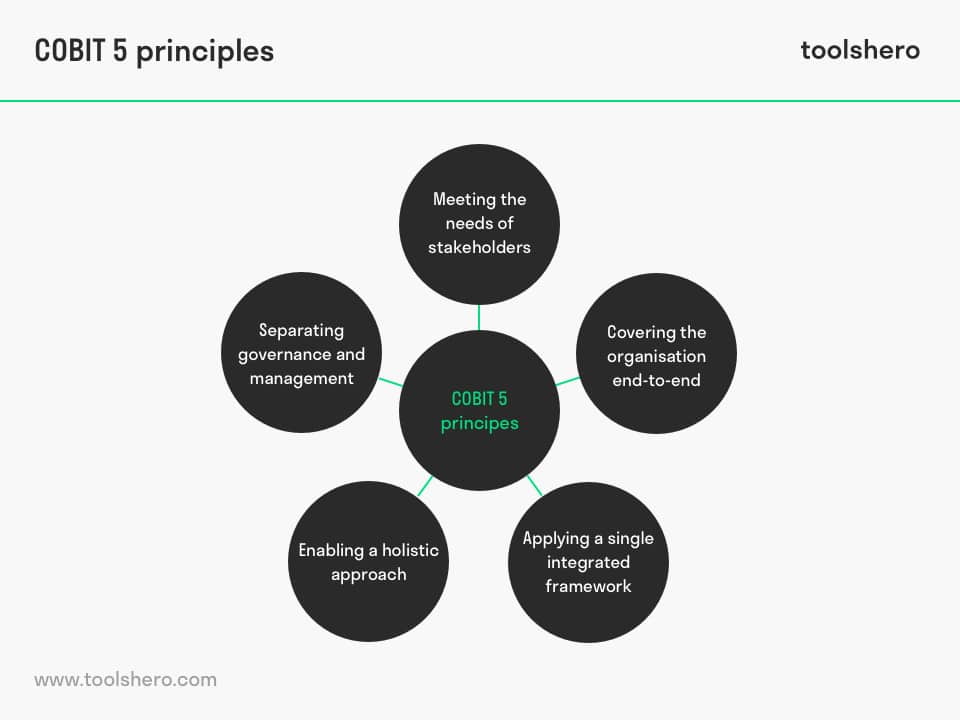
The COBIT 5 Framework Principles
According to COBIT’s developer, ISACA, it helps businesses to maximise value in the area of IT. It does so by creating and maintaining a balance between the achieving of objectives, optimising risk levels, and efficiently assigning and using resources; governance for information technology.
This balance is achieved through five principles. The principles have been developed to be broad and are therefore generic. They meet the requirements of any business, regardless of how large or complex it is.
1. Meeting the needs of stakeholders; the first principle of the COBIT 5 Framework
The first principle of the COBIT formula is meeting the interests and needs of stakeholders. It is based on the idea that businesses exist to create value for stakeholders.
Stakeholders have certain demands, and those demands have to be converted to organisational objectives. When making decisions related to IT management in an organisation, stakeholders have to be informed and involved with this processes.
2. Covering the organisation end-to-end
The second principle emphasises that the control and risk management applies to the whole organisation, including everything. All roles and processes information is associated with have to be included.
3. Applying a single integrated framework
The third principle is using a single integrated framework. This can help organisation get the maximum value from their IT solutions. Furthermore, COBIT can as such be used as an overarching system in combination with frameworks such as BiSL and COSO.
4. Enabling a holistic approach; the fourth principle of the COBIT 5 Framework
The fourth principle is about making a holistic approach possible. That means that so-called enablers are used. These enablers influence whether something works or not. COBIT 5 has seven enablers for improving the Governance of Enterprise IT (GEIT):
- Principles
- Policy
- Frameworks
- Processes
- Culture
- Information
- People
These seven enablers are explained in more detail under the header below.
5. Separating governance and management; the fifth principle of the COBIT 5 Framework
The fifth and final principle of COBIT 5 is about separating governance and management. COBIT emphasises that it’s necessary to make a distinction between governance and management because ISACA believes that these two components require separate structures and processes.
Seven enablers
The goal of COBIT is to optimise the Governance of Enterprise IT (GEIT). In order to achieve this, seven enablers have been defined to support the implementation of COBIT.
1. Principles, policy, and frameworks
The first category of enablers are the principles, policy, and frameworks. Principles and policy help to stimulate a certain desired behaviour. Frameworks help the organisation by establishing a simple guideline for day-to-day management.
2. Processes
The second category of enablers are the processes. Processes have to be designed in such a way that they contribute to achieving the objectives as much as possible. Different organisations have different objectives. Business processes can be adjusted using Business Process Re-engineering (BPR).
3. Organisational structure
The third category of enablers is the organisational structure. Part of that is the policy, the size of the organisation, and the relationship between the IT solutions and the organisation itself. It, for instance, determines the level of specialisation that is required, and how the control can be ideally designed for the organisation type.
4. Culture, ethics, and behaviour
The fourth category is culture, ethics, and behaviour. The culture within a company is an important factor in achieving successes and suffering failures in management activities and governance.
5. Information
The fifth enabler is information. Information is present in any organisation, large or small, and is essential for designing the organisation and its IT solutions. Information is gathered as part of an organisation’s daily activities, and this information is processed in business processes.
6. Services, infrastructure, and applications
The sixth category of enablers are services, infrastructure, and applications. This category applies to governance for IT, because designing and using information systems involves a lot of complex technology.
5. People, skills, and competencies
The seventh category of the COBIT 5 enablers are people, skills, and competencies. It’s basically an enabler for all activities that have to be done in general, but having the right people with the right competencies in the right place might be the most important COBIT enabler.
Advantages of COBIT 5
The main advantage of using COBIT is changing demands, regulations, and risk scenarios of information technology solutions can be met. The company behind the framework supports maximising the value of intellectual property, managing risks, and securing and ensuring compliance through effective IT management.
It also helps businesses to:
- Manage high-quality information to support decisions
- Achieve strategic goals through effective and innovative use of IT
- Achieve excellence in operational process through reliable and effective use of technology
- Keep IT risks at an acceptable level
- Reduce costs for IT solutions and technology
- Support the compliance with laws, as well as regulations and contractual agreements
Now it’s your turn
What do you think? Are you familiar with the explanation of COBIT 5? Is COBIT used in your surroundings? Which of the seven enablers do you think are the most important, and why? Do you have any questions, comments or tips, or anything else to add?
Share your experience and knowledge in the comments box below.
More information
- De Haes, S., Van Grembergen, W., & Debreceny, R. S. (2013). COBIT 5 and enterprise governance of information technology: Building blocks and research opportunities. Journal of Information Systems , 27(1), 307-324.
- Von Solms, B. (2005). Information Security governance: COBIT or ISO 17799 or both?. Computers & Security, 24(2), 99-104.
- Ridley, G., Young, J., & Carroll, P. (2004, January). COBIT and its Utilization: A framework from the literature. In 37th Annual Hawaii International Conference on System Sciences, 2004. Proceedings of the (pp. 8-pp). IEEE.
- Lainhart IV, J. W. (2000). COBIT™: A methodology for managing and controlling information and information technology risks and vulnerabilities. Journal of Information Systems, 14(s-1), 21-25.
How to cite this article:
Janse, B. (2019). COBIT 5 Framework. Retrieved [insert date] from Toolshero: https://www.toolshero.com/information-technology/cobit-5/
Original publication date: 07/31/2019 | Last update: 06/09/2023
Add a link to this page on your website:
<a href=”https://www.toolshero.com/information-technology/cobit-5/)”>Toolshero: COBIT 5 Framework</a>